Stuff The Internet Says On Scalability For September 1st, 2017
Hey, it's HighScalability time:
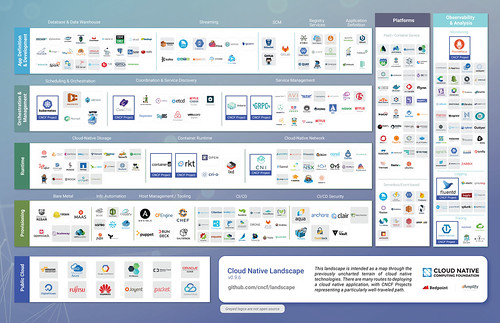
Obviously, cloud native is simplicity itself. (Cloud Native Landscape Project)
If you like this sort of Stuff then please support me on Patreon.
- $10: price for IPv4 address (and falling); 10-15%: better IPv6 network performance; 711M: Record Onliner Spambot Dump; 41.4-tesla: strongest resistive magnet; 85%: cell towers offline due to Hurricane Harvey; 1M: Facebook accounts turned off every single day; 700K: Lyft drivers; $160B: Crypto Market Cap; $1.5M: bounty for iPhone jail break; 2.93M: pirated views of Mayweather-McGregor fight; 465k: people need to update pacemaker firmware; 70,065,920: views of Taylor Swift in 2 days; 2 trillion: kafka messages per day at LinkedIn; $35 billion: saved when planes fly themselves; 990: bird species in North America; 108B: number of people who have ever lived; 500M: DuckDuckGo anonymous searches in one month;
- Quotable Quotes:
- @asymco: The iPhone is not only the best selling product of all time but it may be the most used. 60 trillion minutes a year.
- @Nick_Craver: Stack Overflow Questions (last 30 days): 1,280,911,699 Hits 26.92 ms Avg Render Time 11,040,996,940 SQL Queries 4,489,374,544 Redis Hits
- @GBrayUT: Rough CDN numbers [for Stack Overflow] from bosun ~2000 hits/sec to sstatic at peak. Comes out to another 885 million hits/week, or ~3.8 billion CDN Hits/30 days
- @msuriar: Why is loadshedding such a thing at Google? Because in 2009 we had 3 public visible Gmail outages. #SREcon
- @phoronix: The @AMDRyzen #Threadripper 1950X managing a #Linux kernel build in about 36 seconds, not bad!
- @cmeik: When I told Barbara Liskov that some applications didn't need serializability she gasped.
- Dan Lyons: A century ago, factory workers went on strike to demand better conditions. Today, startup "hustlers" celebrate their own exploitation.
- @nigewillson: Forget 20+ Billion #IOT devices by 2020, imagine the Disruption from 1 billion drones by 2030 ! http://ab.co/2wnLXfi #drones @thomasfrey
- @markcallaghan: Peak write rate might be 20% better in recent MyRocks. FlushWAL might be why
- nnfy: Threadripper is not just about speed. It is about PCIE lanes. Intel has been taking advantage of its monopoly for decades, artificially limiting PCIE lane count, among other things. This may be the start of a new era in computing, allowing GPGPUs to be used more readily, not to mention specific neural network and deep learning applications.
- api: Most ICO projects are complete and utter vapor consisting of nothing more than a stock bootstrap web site and a "white paper" that could have been generated by a Markov chain model using crypto and decentralized systems buzzwords. A few have a bit of code online that doesn't work. Of those that have shipped most of them are unusable, and of those that are usable I am only aware of maybe one or two that are at all interesting. Of those none are very compelling and none are things I couldn't do without. There are literally no hits in this space. It's all junk, and most of it is outright scams. I'd be surprised if a single current generation coin ever actually delivers real ROI.
- @sarahmei: 1. Software is not about rigor. It's about mapping what people want onto what machines can do. It's messy, it's chaotic, it's wonderful.
- @QuinnyPig: #SREcon "How did you get management support for this?" @ING: "We put them into the on-call rotation." Oh my god it's brilliant.
- @PaulDJohnston: You can never know all of AWS. So don't try.
- retox: Only on HN would targeting 100 million devices for a preview be seen as small fry.
- Ann Mutschler: the retina’s 1 million or so ganglion cells are composed of about 20 distinct types. Each plays a slightly different role in transmitting the perception of shape, color, depth, motion and other visual features to the brain.
- Stack Overflow: Python and R are associated with a country’s income. Python is visited about twice as often in high-income countries as in the rest of the world, and R about three times as much.
- Itai Gurari: Human: What is the purpose of existence? Machine: to find out what happens when we get to the planet earth
- @CodeWisdom: "A language that doesn’t affect the way you think about programming is not worth knowing." - Alan Perlis
- Team Shellphish: Kubernetes (kubernetes.io) - The distribution of docker containers across our cluster, and the load-balancing and failover of resources, was handled by kubernetes. In our final setup, the Mechanical Phish was so resilient that it could probably continue to function in some form even if the rack was hit with a shotgun blast.
- Jeff Dorsch: What is clear, given the focus of presentations, is that the bleeding edge of computing has shifted significantly in the past 12 months. While performance and power are still critical elements, the primary concern is no longer how to cram more transistors on a piece of silicon or how to put multiple chips together. It is now much more geared toward new architectures that can bridge the digital and physical worlds.
- Karen Stabiner: “At least once a week, I get something about a new start-up with a new gadget that’s going to make our lives so much better,” said Sisha Ortuzar, Mr. Colicchio’s partner at ‘Wichcraft. “They’re distractions. We just want to get back to making sandwiches.”
- Lila MacLellan: And everything changed. Pre-Keith, Dwyer explains, “it was very clear no one took us seriously and everybody thought we were just idiots.” When “Keith” contacted collaborators, Gazin says, “they’d be like ‘Okay, bro, yeah, let’s brainstorm!’”
- userbinator: Looks like those Seagates are still disappointingly failure-prone, while HGST remains the most reliable.
- ISTC: network bandwidth already available today can be on par with the main memory bandwidth.
- Michael P Frank: This idea of reversible computing goes to the very heart of thermodynamics and information theory, and indeed it is the only possible way within the laws of physics that we might be able to keep improving the cost and energy efficiency of general-purpose computing far into the future.
- jcampbell1: Grammarly absolutely crushed it with Adwords on the content network. There was so much cheap inventory they were able to buy such as on dictionary sites.
- There is a bit of a Y Combinator attitude against buying advertising to build a startup. If it ain't viral, then the product isn't good enough.
- jedberg: [Amazon] absolutely will not look at your data under any circumstance, even if you specifically ask them to. Multiple times I was trying to troubleshoot an issue and asked them to "just log into the database" and they said they have very strict policies against that. There is no way they have any of Target's data.
- @benthompson: The fundamental failing in discipline after discipline is the overvaluing of what can be measured, and the dismissal of what can not.
- dmitrygr: I read the paper. Still not sure how this [Mercury Protocol: Communication Platform Built on the Ethereum Blockchain] solves anything besides transferring wealth from the gullible to the authors:
- @Nick_Craver: Code review just now: a errant boolean check in our Master.cshtml can cost upwards of 100 million hits to redis a day. Crazy to think about.
- moxious: First, the idea of running a distributed ledger to keep track of burger points. This is the tech equivalent of using a bazooka to address an ant problem.
- mcgarnagle: Say what you will, at least the whoppercoins are backed by something that has survived the test of time, the whopper.
- contingencies: For financial transaction services I can recommend sharding first by customer, then by ledger. As a result, instead of enforcing double-entry book-keeping standards within a single database, do it at an application-specific middleware server layer to enforce only the guarantees you need.
- @stevesi: AR by itself isn't a platform but it is precisely the kind of platform feature that makes cross-platform impossible.
- Camillo Bruni: Changing the property or element type typically causes V8 to create a different HiddenClass which can lead to type pollution which prevents V8 from generating optimal code
- redwood: I lived in a country where everyone has a power generator in their building. Let's just say the quality of life was significantly lower. This cloud shift is like an unstoppable tidal wave. I'm always surprised when I hear people with your argument [that the cloud is not a utility]
- Tim Harford: It’s not simply that Blade Runner fumbled its futurism by failing to anticipate the smartphone. That’s a forgivable slip, and Blade Runner is hardly the only film to make it. It’s that, when asked to think about how new inventions might shape the future, our imaginations tend to leap to technologies that are sophisticated beyond comprehension.
- @krishnan: For Google, Kubernetes is just an enterprise trojan horse to onboard customers to their cloud
- @roboYeti: Started playing with KSQL. Joining tables with streams from my Kafka topics -no problem. @jaykreps it's awesome piece of Engineering. Thanks
- Tom Griffiths: This is a moment where we are starting to recognize that we're going to need to interact with systems that, at least in restricted domains, are going to be smarter than us. Thinking about how to design those interfaces between humans and machines in ways that make it possible for us to interact with those systems in a way that allows us to function effectively is an important research challenge, and a significant social challenge.
- mrmrcoleman: At a previous company we had a 'farm' of test phones that we used for testing new versions of software. A large number of those test were 'stress testing' which would probably be analogous to the sort of load you would have it they were to be treated as a 'datacenter'. Based on that I'm pretty sure that the biggest issue with managing the cluster would be the extremely high failure rate. That's not to say that this won't work because I haven't done the maths, but it kid a unique challenge.
- Michael Mullany: What I take away from my analysis of these Hype Cycles is not just how difficult it is to make predictions, and how much wasted effort goes into technologies that doesn't tend to work, but also how exciting and wondrous is the progress that we've made in technology. The labor of the last two decades has given rise to an Age of Wonders
- How to beat the AWS Lambda deployment limits. The secret? Upload from S3. You get 250 MB uncompressed instead of the documented limit of 50 MB. But what is the startup time for something that big?
- You think you know, but you don't know. 8 Lessons from 20 Years of Hype Cycles: We're terrible at making predictions. Especially about the future; An alarming number of technology trends are flashes in the pan; Lots of technologies just die. Period; The technical insight is often correct, but the implementation isn't there; We've been working on a few core technical problems for decades; Some technologies keep receding into the future; Lots of technologies make progress when no-one is looking; Many major technologies flew under the Hype Cycle radar.
- It's like we each have a data doppelganger leading a completely different life than we do. Inside the Massive 711 Million Record Onliner Spambot Dump: It took HIBP (Have I been pwned before) 110 data breaches over a period of 2 and a half years to accumulate 711m addresses and here we go, in one fell swoop, with that many concentrated in a single location. It's a mind-boggling amount of data...that's the unfortunate reality for all of us: our email addresses are a simple commodity that's shared and traded with reckless abandon, used by unscrupulous parties to bombard us with everything from Viagra offers to promises of Nigerian prince wealth. That, unfortunately, is life on the web today.
- California CPA firm reports data breach. As the malware industry matures, attacks are becoming smarter and more targeted. We're out of the kids stealing a car for a joy ride phase and into the ring of professional car thieves phase where specific cars are targeted, stolen, and driven directly into waiting shipping containers for sale overseas. Unfortunately, businesses are not keeping pace in this back and forth war of attrition.
- Microsoft is making their Orleans Transactions publicly available. They're moving from a locking and dependency injection concurrency control approach to a timestamp based method. No reason given as to why. galvesribeiro asks a good question: I don't understand the change from locking to timestamp. Are you saying that you are using optimistic concurrency on this implementation instead of the weak-lock we have first phase of 2PC? If that is the case, doesn't it break all the "new" strategy defended by @philbe paper?
- The Amish use a canary approach when choosing which technologies to adopt. Kevin Kelley, “Wired” Founding Executive Editor & “The Inevitable” author/futurist, explains how on This Week In Startups. The Amish aren't luddites, they're slow followers, selective curators who admit technologies into their portfolio based on deeply held core principles. Individuals don't choose which technologies to adopt, the community decides based on how it impacts the family and community. They ask: will this technology allow me to spend more time with my family? Will this technology increase the strength of our community? Cell phones are allowed, smart phones are not. Cars were rejected because they let people travel far away from family and community. A horse & buggy keeps everyone within a 15 mile radius. Eating meals together as a family is important, so the Amish create backyard businesses. Using a CNC milling machine is OK because it keeps the family together. Solar panels and chain saws are also OK. They have Amish computers, which are computers without an internet connection. And the computer is used in the office only, not at home. How do they pick which technologies to use? They try them. One or two early adopter families use a technology and they are observed. If it's deemed the technology hurts the family or the community, then the technology is voted off the island.
- Hipmonk on A Fare Cache in a Sharded Data Cluster: So the problem becomes, how to put all these fares into a database that easily scales?...Now for any modern database, 100 million data points is pretty simple. What makes the problem interesting is the frequency of data refresh, and the complexity of the searches...Citus interacts with the PostgreSQL query planner and executor to permit distributed tables over a cluster of servers. It also provides a set of SQL functions to manage the cluster...A sharded architecture works well for this problem...As long as all data relationships can be expressed on a per-shard basis, queries will run in parallel, allowing read and write scale.
- Are we ready yet for a P2P browser based CDN, that enhances existing web-content delivery transparently? Cache Me If You Can. Deploy a global, private CDN on your lunch break. Edgemesh says yes, lots of folks on HackerNews say no. Why now? Uplink capacity has increased, there are now enough edge devices, nodes stay online long enough, there's enough spare disk capacity, service-worker framework enable asset interception, WebRTC facilitates browser-to-browser asset replication. The result: nearly 50% reduction in average load times. Why the negative sentiment? chrissnell: Ugh, I hate these P2P "CDNs". A few years back, CNN tried this for their streaming video with technology from a company called Octoshape. Users (including myself) were unwittingly conned into accepting the plugin in order to watch live video. This created a huge mess for big corporate IT departments, who suddenly had hundreds or thousands of desktop machines streaming out video whenever there was a major news event. willitpamp573: Seeding data to random peers will make my internet slower, not faster. I don't want to seed. fundabulousrIII: You want to push CDN bandwidth constraints onto consumer networks in some p2p model and trust the content coming out of it? The idea is ridiculous in every aspect except for those who don't know anything that are buying this paradigm. mattbillenstein: BitTorrent tried to market this product when video streaming on the web was still fairly new under the BitTorrent DNA name. As I recall, over the year it was being developed, bandwidth prices dropped something like 80% which made the market for it pretty much evaporate at that time.
- We have no idea what's inside any thing we use. None. Researchers built an invisible backdoor to hack AI’s decisions: The idea is that, a hacker could train a model to do something unusual when it identifies a specific use case. For example, train a visual sign identification model that, when a stop sign has graffiti that says "HEY!" shut down the car. Now, if you want to stop someone, and you know their route to work, you just spray paint "HEY!" on the sign the an hour before they drive by. Also, Secret chips in replacement parts can completely hijack your phone’s security. Also also, Advisory: AccuWeather iOS app sends location information to data monetization firm.
- Shattered Trust: When Replacement Smartphone Components Attack: Phone touchscreens, and other similar hardware components such as orientation sensors, wireless charging controllers, and NFCreaders, are often produced by thirdparty manufacturers and not by the phone vendors themselves. Third-party driver source code to support these components is integrated into the vendor’s source code. In contrast to “pluggable” drivers, such as USB or network drivers, the component driver’s source code implicitly assumes that the component hardware is authentic and trustworthy. As a result of this trust, very few integrity checks are performed on the communications between the component and the device’s main processor.
- Lyft with an eloquent explanation of why they like SaltStack. SaltStack as an Alternative to Terraform for AWS Orchestration: A tenet of our design is that AWS already has our infrastructure’s state, and that we shouldn’t track state separately, as it will diverge. Additionally, we want to be able to run our orchestration in parallel across service deploys, and potentially across an arbitrary number of services at a time...There are, of course, some downsides to this design. Since the system references other resources loosely, we can’t automatically determine the ordering in which the states need to be applied...Another tenet of our design is that we want our service teams to be able to manage their orchestration code inside of their own service repositories...Our primary concern with CF was that it may automatically perform a destructive action upon detection of a change in a resource definition...Over time, as we added features, there were some actions that were so common that we wanted them applied by default for every instance of that resource.
- Walmart Taps Nvidia for Massive Cloud to Take on Amazon. Target is plotting a big move away from AWS as Amazon takes over retail (using Spinnaker from Netflix). Just a reminder, the continental strategy employed by Napolean to cut off trade with England was his ultimate downfall. An anti-AWS strategy will cause only self-inflicted wounds. After all, Apple still buys critical parts from Samsung. Saint Helena is no place to die.
- Show 354: Future Of Networking With Fred Baker. The IPv4 network is measurably slowing down because of the overhead of multiplexing NAT. Now that we're moving to multi-gigabit internet gateways, NAT adds a significant performance penalty in terms of latency, delay, etc. Removing NAT makes connectivity more reliable and faster, so IPv6 performs 10-15% better. Enterprises are the laggards in adopting IPv6, everyone else on the adoption train. Interesting powerful idea of running a /64 subnet to each chassis, instead of using neighbor discovery, the counter part to ARP, use BGP; the value is instead of being limited by UDP/TCP port numbers, IPv6 addresses could be used to get to containers or to get to applications, treating each chassis as a LAN full of endpoints.
- Looks great for those who like a more hands on approach. Building a Modern Computer from First Principles: The site contains all the software tools and project materials necessary to build a general-purpose computer system from the ground up. We also provide a set of lectures designed to support a typical course on the subject. Also, A computer science course for craftsman.
- OK, you know the world is going in a weird direction when authors talk about selling books using the blockchain. AskALLi: Self-Publishing Advice Podcast and Indie Authors: Are We Ready for Self-Publishing 3.0?. The hope is for indie authors to create an author led value chain, where authors get paid first, thus breaking the strangle hold Amazon and trad have on the publishing industry. Self-publishing 1.0 was desktop publishing. Self-publishing 2.0 is the internet and social media which have allowed authors to directly target consumers. Self-publishing 3.0 is money going to the author first. I think they're missing the corrosive role of the middle-person on the internet. Amazon wins because they control access to the customer. That's why Amazon is so valuable. Authors pay their Amazon tax to be put in front of a huge and hungry customer base. Unfortunately, the blockchain doesn't change that relationship at all. You can't just pluck one part of the value chain out and optimise that. It's the ecosystem that has value. The age old question for content creators is: how do I get my content in front of buying customers? Amazon has the answer.
- Looking at Disk Utilization and Saturation: The Utilization metric (as reported by iostat and by PMM) is not very helpful for showing true storage utilization, as it only measures the time when there is at least one request in flight...Unlike a CPU, Linux tools do not provide us with information about the structure of the underlying storage and how much parallel load it should be able to handle without saturation...Avg Response Time is a great metric for looking at saturation, but as with the response time you can’t say what response time is good or bad for this device.
- Another sign of world weirdness. Burger King launches WhopperCoin crypto-cash in Russia. At first this seems absurd, but ringaroundthetx helps us make sense of it: They are using the Waves platform, which has very easy 1-click asset creation. Waves is also Proof of Stake, so there's no mining involved. This gives the transparency benefits and distribution benefits, without any of the overhead. Regarding distribution, waves platform has a culture of airdrops in it. I find Waves fun. Between leasing, the decentralized exchanges, the airdrops, the dividends, and finding out about the assets that got airdropped or dividended to you, I find myself in the app quite often unintentionally. The airdropped assets are mostly worthless, but the descriptions of the assets are interesting. I would say the fun aspect is different than other cryptocurrencies. Its like finding random stuff in Skyrim, keeps me coming back. For reference, I buy Waves and purchase Waves Community Tokens (WCT) on the decentralized exchange. Most airdrops go to WCT holders, they just take a record of the blockchain and send to all address with WCT balances. I lease my remaining Waves to the pools FountainPerpetua and WavesGo. There are plenty of other pools to lease to. Pools give payments in the form of Waves, because thats what they earn, but they also have the option of giving payments in other assets too, they just need to remain competitive. So I typically earn Waves, Waves Community Tokens and Miners Rewards tokens. The WavesGo pool gives WavesGo tokens which are actual shares and actual securities. WavesGo pools distributes more of its own earnings to all WavesGo holders. You can buy and sell more WavesGo shares on the decentralized exchange.
- Completely wrong. Sounds nothing like the original Klingon. Hear What Hamlet, Richard III & King Lear Sounded Like in Shakespeare’s Original Pronunciation.
- The End of Slow Networks: It’s Time for a Redesign: we believe there is a need to critically rethink the entire distributed DBMS design – from the architecture to the guts – to take full advantage of the next generation of network technology...In the traditional architecture, a transaction is first sent by the client (e.g., an application server) to a transaction manager (TM), which then initiates a 2-phase-commit protocol using messages. In contrast, in the NAM architecture the client modifies directly the remote memory addresses using special primitives...we propose a novel Network-Attached-Memory (NAM) architecture, which logically decouples compute and storage. In this architecture, the NAM servers provide a shared distributed memory pool abstraction that can be accessed from any compute node...the redesigned architecture [NAM] achieves a stunning 1.79 million distributed transactions with 70 clients and shows a linear scaling behavior with an increasing number of clients, whereas the more traditional approaches achieve not more than 32,000 distributed transactions. Even more surprising, the faster network without a redesign of the system decreases the transaction throughput from 32,000 distributed transactions to 24,000 transactions.
- When is auto-scaling not? When triggering thresholds are set too high. Don't be so cheap! Load testing reveals issues in the cloud: we found that the way auto-scaling had been configured meant that end-user experience would have been extremely poor...auto-scaling had been configured to bring more resources to bear from 70% CPU utilisation, but only if CPU was at 70% or greater for 10 minutes, so we had found the reason why more servers had not spun up...a new rule that stated that if CPU is 80% or greater, spin up the extra resources immediately. This dynamic change to configuration proved effective as CPU started to climb again
- Nice overview. SRECON EUROPE 2017 -- DAY 1. SRECON EUROPE 2017 -- DAY 2.
- Gives ransomware a dark new twist. patients told to visit doctor to patch critical pacemaker vulnerability. The update will require patients to visit a clinic where doctors will put the pacemakers in backup mode while the firmware is being patched. Doesn't this mean we are cyborgs now?
- What a glorious world it will be. The next wave of computing: Crypto tokens for protocols will become as ubiquitous as software licenses and terms-of-service agreements for cloud services: to use the software in decentralized computing you’ll need the respective token. Crypto economy will reshape the entire lifecycle of tech companies. Currently, they get their start on Sand Hill Road and end up on Wall St. Soon, they’d start anywhere and end up on token exchanges. Also, Storj: Not a Dropbox Killer.
- Once your SIM is hijacked, you're toast. Security Now 626 Shattering Trust. The attacker can access Facebook Messenger, try to scam everyone in your contact list, and all sorts of other evil doer things. The takeaway lesson: While it may be unlikely for everyone, targeted attacks CAN be quite powerful and successful. The new hacking method is to arrange to take over the communications channel used for account verification and/or second factor authentication. This is why time-based One Time Passwords, NOT communications-based One Time Passwords, are the only safe choice to make when a choice can be made
- The Calculus of Service Availability: Internally at Google, we use the following rule of thumb: critical dependencies must offer one additional 9 relative to your service—in the example case, 99.999% availability—because any service will have several critical dependencies, as well as its own idiosyncratic problems. This is called the "rule of the extra 9."
- enterprise drives == consumer drives. Backblaze with Hard Drive Stats for Q2 2017: The enterprise drives have 363,282 drives days and an annualized failure rate of 1.61%. If we look back at our data, we find that as of Q3 2016, the 8 TB consumer drives had 422,263 drive days with an annualized failure rate of 1.60%. That means that when both drive models had a similar number of drive days, they had nearly the same annualized failure rate.
- BGP Persistent Oscillation: The reason the ADD_PATH extension solves this problem is that A and D both have a full view of every exit point once each BGP speaker sends every route to each destination, rather than just the best path.This is, in effect, another instance of the inconsistency of a distributed database causing a persistent condition in a control plane. In (loosely!) CAP theorem terms, distributed routing protocol always choose accessibility (the local device can read the database to calculate loop free paths) and partitioning (the database is always copied to every device speaking the protocol) over consistency—eventually, or “not always,” consistent databases will always be the result of such a situation.
- Cost/Benefit Analysis of a MySQL Index: So we can see in this case, the index created a delay of 16.8 ms in a half-hour timeframe, but saved 150 ms in reads. It is also impressive that the write index added very little time – 70 microseconds – but saved so much time – 1 millisecond – that there were 16 times the number of writes than reads, but we still had huge improvement, especially given the cost.
- A good whack at explaining Event Sourcing: What it is and why it's awesome. As always, when deriving current state from events, you had better make sure you capture every event in the right order, or you are are totally screwed.
- State of IPv6 Deployment 2017: As noted, IPv6 has been a project in development or test for a long time, but is now a present reality. To pick one country, Trinidad and Tobago use IPv6 for a significant fraction of their traffic. This demonstrates that IPv6 is not a research project or “only in the most developed countries”; Trinidad and Tobago is among what the UN calls “Small Island Developing States”, and an object of UN development funding. But Google asserts that 15% of accesses from there to Google use IPv6, and Akamai asserts that 20-30% of their traffic to Trinidad and Tobago uses IPv6. Of the G20 nations, 18 have measurable IPv6 traffic, and 12 are in the list of 37 nations using Google for more than 5% of their traffic. From an adoption perspective, IPv6 has now emerged from the “Innovators” and “Early Adoption” stages, and is moving into the “Early Majority”. The price of an IPv4 address is near its projected peak, and cloud hosting providers are starting to charge for IPv4 while leaving IPv6 free.
- Well explained with code examples. Higher Order Functions: Using Filter, Map and Reduce for More Maintainable Code. It dissapoints me that I still find the for loop code easier to understand.
-
facebookincubator/FCR: A thrift service to run commands on heterogeneous Network devices with configurable parameters. It scales to a large number of devices.
-
Developer-Y/cs-video-courses: List of Computer Science courses with video lectures.
-
JamesMilnerUK/cheap-ruler-go: A collection of very fast approximations to common geodesic measurements. Useful for performance-sensitive code that measures things on a city scale
-
OrpheusDB: a database system that supports versioning capabilities. Since OrpheusDB is built on standard relational databases, it inherits much of the same benefits of relational databases, while also compactly storing, keeping track of, and recreating versions on demand.
-
Retrospective Lightweight Distributed Snapshots Using Loosely Synchronized Clocks: In order to take a consistent snapshot of a distributed system, it is necessary to collate and align local logs from each node to construct a pairwise concurrent cut. By leveraging NTP synchronized clocks, and augmenting them with logical clock causality information, Retroscope provides a lightweight solution for taking unplanned retrospective snapshots of past distributed system states. Instead of storing a multiversion copy of the entire system data, this is achieved efficiently by maintaining a configurable-size sliding window-log at each node to capture recent operations
-
Price-Optimal Querying with Data APIs: The key idea behind our approach is the notion of refunds: buyers buy data as needed but have the ability to ask for refunds of data that they had already purchased before. We show that our techniques can provide significant data cost savings while reducing overheads by two orders of magnitude as compared to the state-of-the-art competing approaches.
-
Write-Behind Logging: This paper explores the changes that are required in a DBMS to leverage the unique properties of NVM in systems that still include volatile DRAM. We make the case for a new logging and recovery protocol, called write-behind logging, that enables a DBMS to recover nearly instantaneously from system failures. The key idea is that the DBMS logs what parts of the database have changed rather than how it was changed. Using this method, the DBMS flushes the changes to the database before recording them in the log. Our evaluation shows that this protocol improves a DBMS’s transactional throughput by 1.3×, reduces the recovery time by more than two orders of magnitude, and shrinks the storage footprint of the DBMS on NVM by 1.5×.
-
Towards Deploying Decommissioned Mobile Devices as Cheap Energy-Efficient Compute Nodes: This work proposes creating a compute dense server built out of used and partially broken smartphones (e.g. screen can be broken). This work evaluates the total cost of ownership (TCO) benefit of using servers based on decommissioned mobile devices and analyzes some of the architectural design trade-offs in creating such servers.
Hey, just letting you know I've written a new book: A Short Explanation of the Cloud that Will Make You Feel Smarter: Tech For Mature Adults. It's pretty much exactly what the title says it is. If you've ever tried to explain the cloud to someone, but had no idea what to say, send them this book.
I've also written a novella: The Strange Trial of Ciri: The First Sentient AI. It explores the idea of how a sentient AI might arise as ripped from the headlines deep learning techniques are applied to large social networks. Anyway, I like the story. If you do too please consider giving it a review on Amazon.
Thanks for your support!




